
|
|





 |
|
||||||||
 |
 |
 |
 |
||||||

|
|||||||||
|
|
  |
 10 Sep 2014, 10:41 AM 10 Sep 2014, 10:41 AM
Post
#1
|
|||||||||||||||||||||
|
Member Group: Members Posts: 40 Joined: 5-September 14 Member No.: 76102 Gender:  |
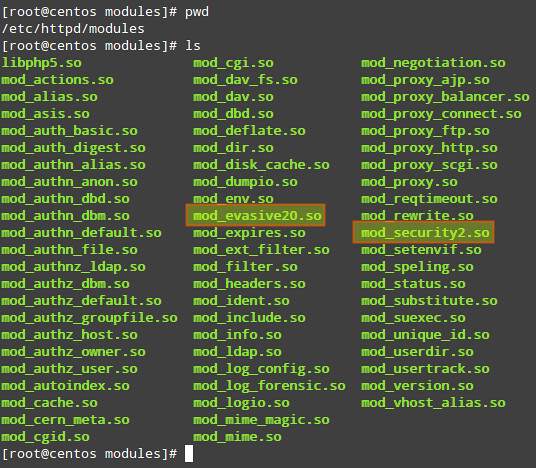
Web server security is a vast subject, and different people have different preferences and opinions as to what the best tools and techniques are to harden a particular web server. With Apache web server, a great majority of experts -if not all- agree that mod_security and mod_evasive are two very important modules that can protect an Apache web server against common threats. In this article, we will discuss how to install and configure mod_security and mod_evasive, assuming that Apache HTTP web server is already up and running. We will perform a demo stress test to see how the web server reacts when it is under a denial-of-service (DOS) attack, and show how it fights back with these modules. We will be using CentOS platform in this tutorial. Installing mod_security & mod_evasiveIf you haven't enabled the EPEL repository in your CentOS/RHEL server, you need to do so before installing these packages.# yum install mod_security # yum install mod_evasive After the installation is complete, you will find the main configuration files inside /etc/httpd/conf.d: 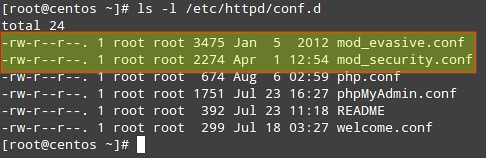 Now you need to make sure that Apache loads both modules when it starts. Look for the following lines (or add them if they are not present) in mod_security.conf and mod_evasive.conf, respectively:
In the two lines above:
 Now restart Apache web server: # service httpd restart Configuring mod_securityIn order to use mod_security, a Core Rule Set (CRS) must be installed first. Basically, a CRS provides a web server with a set of rules on how to behave under certain conditions. Trustwave's SpiderLabs (the firm behind mod_security) provides the OWASP (Open Web Application Security Project) ModSecurity CRS.To download and install the latest OWASP CRS, use the following commands. # mkdir /etc/httpd/crs # cd /etc/httpd/crs # wget https://github.com/SpiderLabs/owasp-modsecurity-crs/tarball/master # tar xzf master # mv SpiderLabs-owasp-modsecurity-crs-ebe8790 owasp-modsecurity-crs Now navigate to the installed OWASP CRS directory. # cd /etc/httpd/crs/owasp-modsecurity-crs In the OWASP CRS directory, you will find a sample file with rule (modsecurity_crs_10_setup.conf.example). 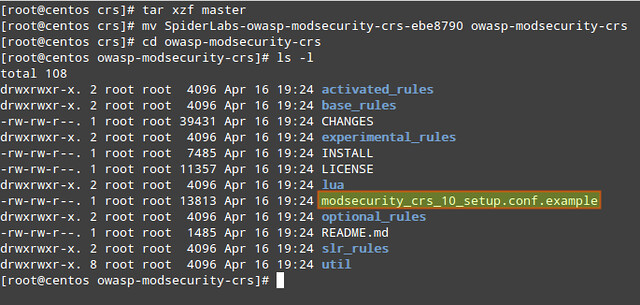 We will copy its contents into a new file named (for convenience) modsecurity_crs_10_setup.conf. # cp modsecurity_crs_10_setup.conf.example modsecurity_crs_10_setup.conf To tell Apache to use this file for mod_security module, insert the following lines in the /etc/httpd/conf/httpd.conf file. The exact paths may be different depending on where you unpack the CRS tarball.
Last, but not least, we will create our own configuration file within the modsecurity.d directory where we will include our chosen directives. We will name this configuration file xmodulo.conf in this example. It is highly encouraged that you do not edit the CRS files directly but rather place all necessary directives in this configuration file. This will allow for easier upgrading as newer CRSs are released. # vi /etc/httpd/modsecurity.d/xmodulo.conf
You can refer to the SpiderLabs' ModSecurity GitHub repository for a complete guide of configuration directives. Don't forget to restart Apache to apply changes. Configuring mod_evasiveThe mod_evasive module reads its configuration from /etc/httpd/conf.d/mod_evasive.conf. As opposed to mod_security, we don't need a separate configuration file because there are no rules to update during a system or package upgrade. The default mod_evasive.conf file has the following directives enabled:
Here are other useful directives for mod_evasive: 1) DOSEmailNotify: Sends an email to the address specified whenever an IP address becomes blacklisted. It needs a valid email address as argument. If SELinux status is set to enforcing, you will need to grant the user apache SELinux permission to send emails. That is, run this command as root: # setsebool -P httpd_can_sendmail 1 Then add this directive in the mod_evasive.conf file:
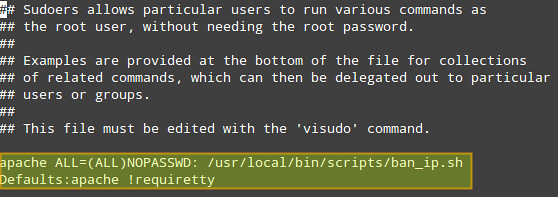
2. DOSSystemCommand: Executes a custom system command whenever an IP address becomes blacklisted. It may come in handy to add firewall rules to block offending IPs altogether.
Don't forget to update sudo permissions to run our script as apache user: # vi /etc/sudoers
 Simulating DoS AttacksWe will use three tools to stress test our Apache web server (running on CentOS 6.5 with 512 MB of RAM and a AMD Athlon II X2 250 Processor), with and without mod_security and mod_evasive enabled, and check how the web server behaves in each case. Make sure you ONLY perform the following steps in your own test server and NOT against an external, production web site. In the following examples, replace http://centos.gabrielcanepa.com.ar/index.php with your own domain and a file of your choosing. Linux-based tools1. Apache bench: Apache server benchmarking tool.# ab -n1000 -c1000 http://centos.gabrielcanepa.com.ar/index.php
Windows-based tools1. Low Orbit Ion Cannon (LOIC): a network stress testing tool. To generate a workload, follow the order shown in the screenshot below and DO NOT touch anything else 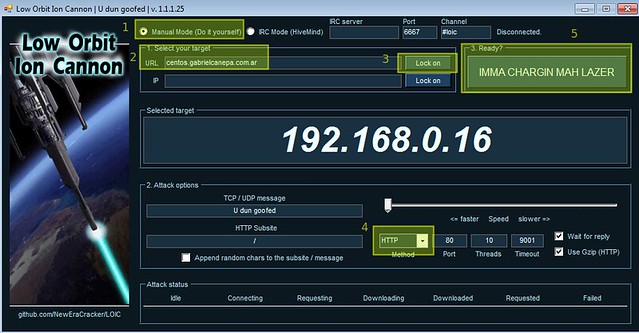 Stress Test ResultsWith mod_security and mod_evasive enabled (and the three tools running at the same time), the CPU and RAM usage peak at a maximum of 60% and 50%, respectively for only 2 seconds before the source IPs are blacklisted, blocked by the firewall, and the attack is stopped.On the other hand, if mod_security and mod_evasive are disabled, the three tools mentioned above knock down the server very fast (and keep it in that state throughout the duration of the attack), and of course, the offending IPs are not blacklisted. ConclusionWe can see that mod_security and mod_evasive, when properly configured, are two important tools to harden an Apache web server against several threats (not limited to DoS attacks) and should be considered in deployments exposed on the Internet. *Source: http://xmodulo.com/2014/09/harden-apache-web-server-mod_security-mod_evasive-centos.html |
||||||||||||||||||||
|
|
  |

|
Lo-Fi Version | Time is now: 19th April 2024 - 07:03 AM |
| Skin and Graphics by Dan Ellis and Anubis. Hosting by Forums & More � 2005-2011. |